Key Points
Hackers are smart. If you leave a gap in your defences, they can find it. As your networks, cloud environments and tech stacks change and grow, vulnerabilities and security loopholes tend to creep in.
Attacks are increasingly automated and indiscriminate. And if hackers are using automated tools to make their work easier, you should too. Automated and continuous coverage was once ‘nice to have’, now it’s a ‘must have’.
That’s why we’ve built a new Premium plan. A plan with powerful new capabilities and automated scanning for continuous coverage that increases visibility, minimizes how long you’re exposed, and reduces the time to remediate. It’s the next step in the evolution of vulnerability management.
Monitor your entire attack surface
The time cyber criminals take to exploit vulnerabilities is shrinking. As defenders, all of us need to make their window of opportunity as small as possible. Our new Premium plan is designed to do that, and move you further down the path of continuous cyber security.
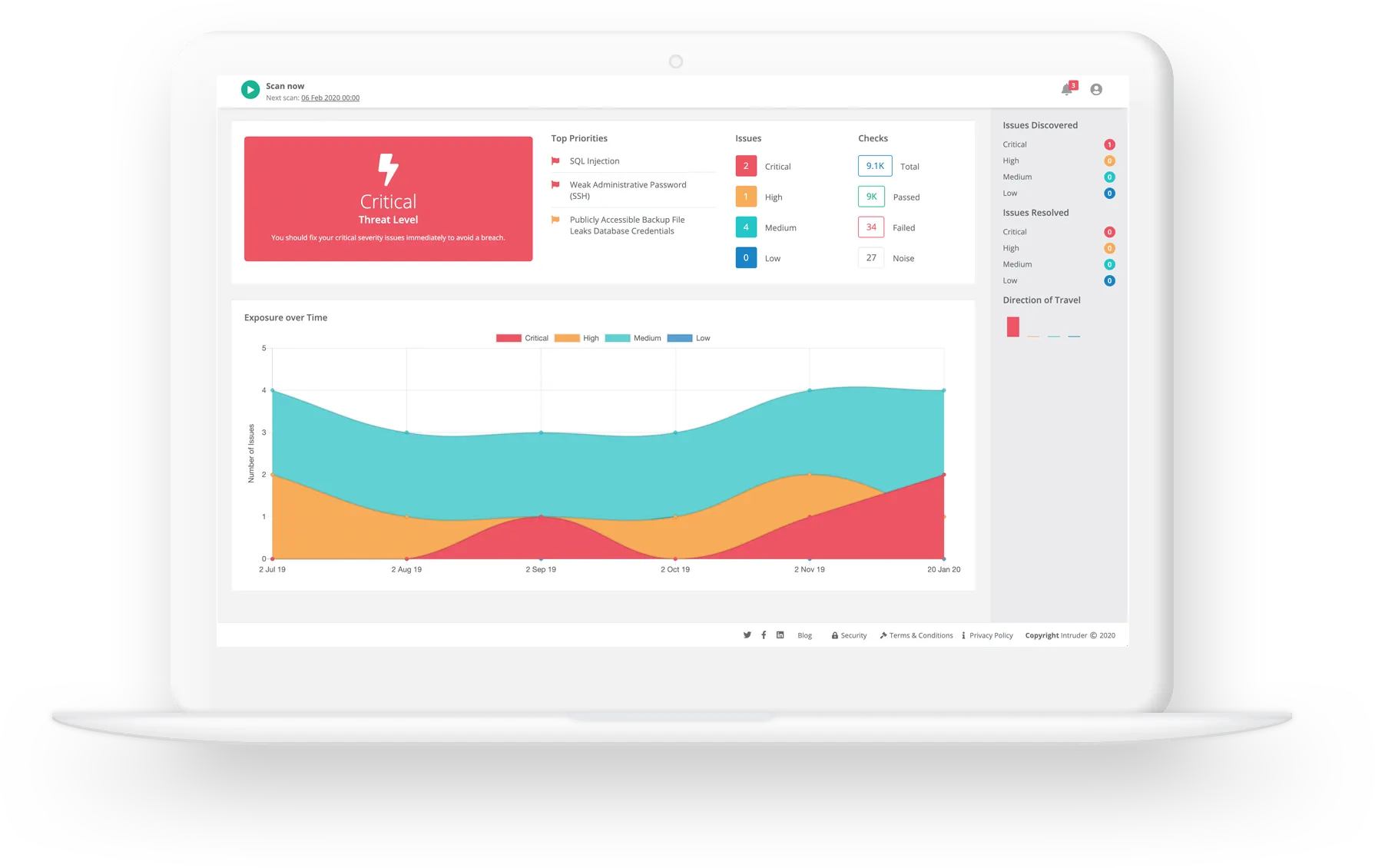
With Premium, your attack surface is scanned every day to see if new services have gone live or offline. If the scan identifies a new target, a licence will be assigned (if available) and the target will automatically be scanned for vulnerabilities. If you don’t have a licence, we’ll let you know. After every scan, Network View will be updated with a summary and any new results.
.png)
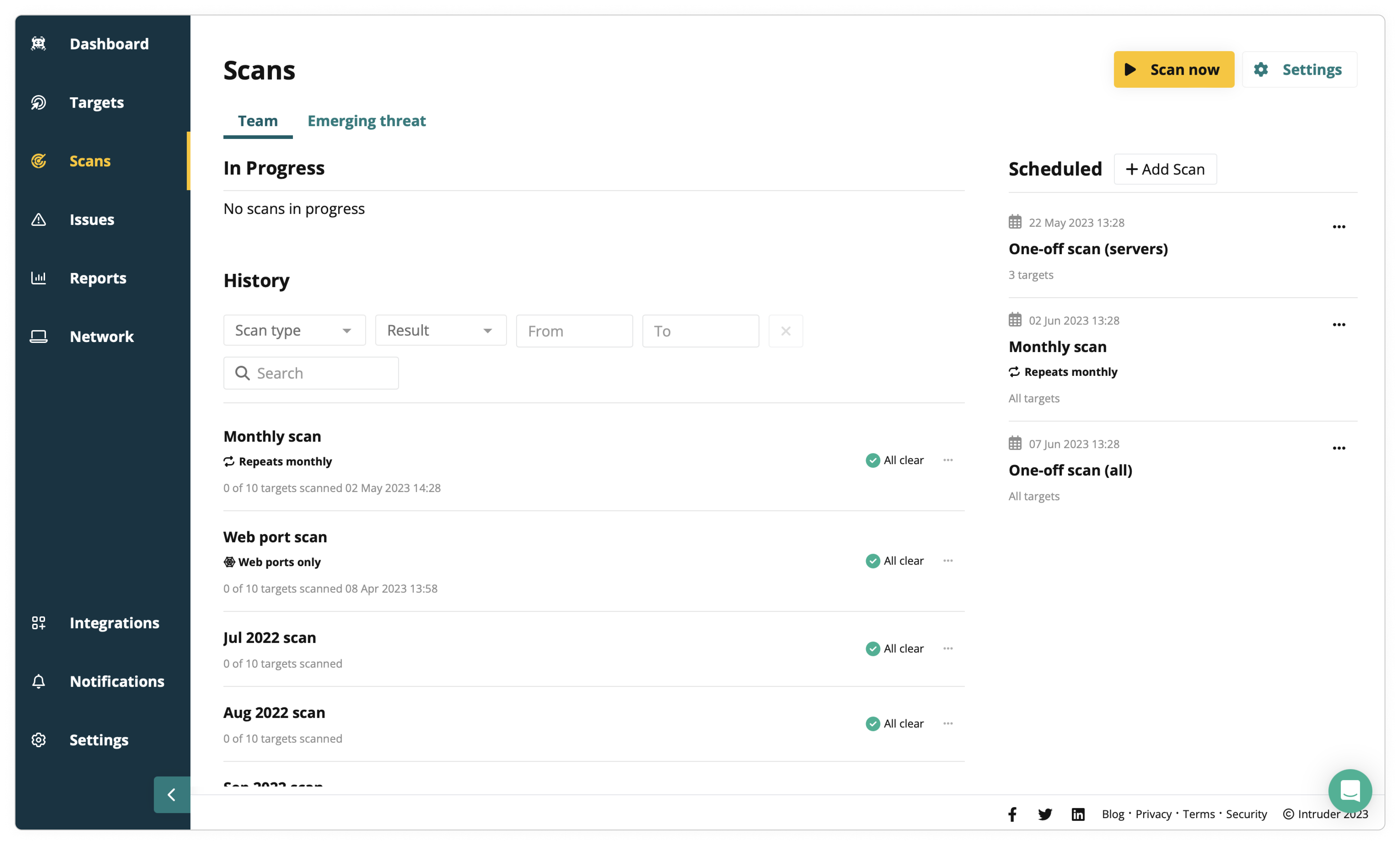
This continuous network scanning shows exactly what your external attack surface looks like, what’s exposed to the internet, and what an attacker can see. It increases the visibility and transparency of your network, so you can minimize the risk of attack by removing things that don’t need to be there – like an admin panel for a networking device which is exposed to the internet:

While Intruder details these issues specifically, most scanners simply show them as an “informational” issue that can easily get lost in the noise of all the other informational issues in your report. Automatically kicking off a vulnerability scan as soon as a scan detects a network change is a real game changer.
Close the window on hackers
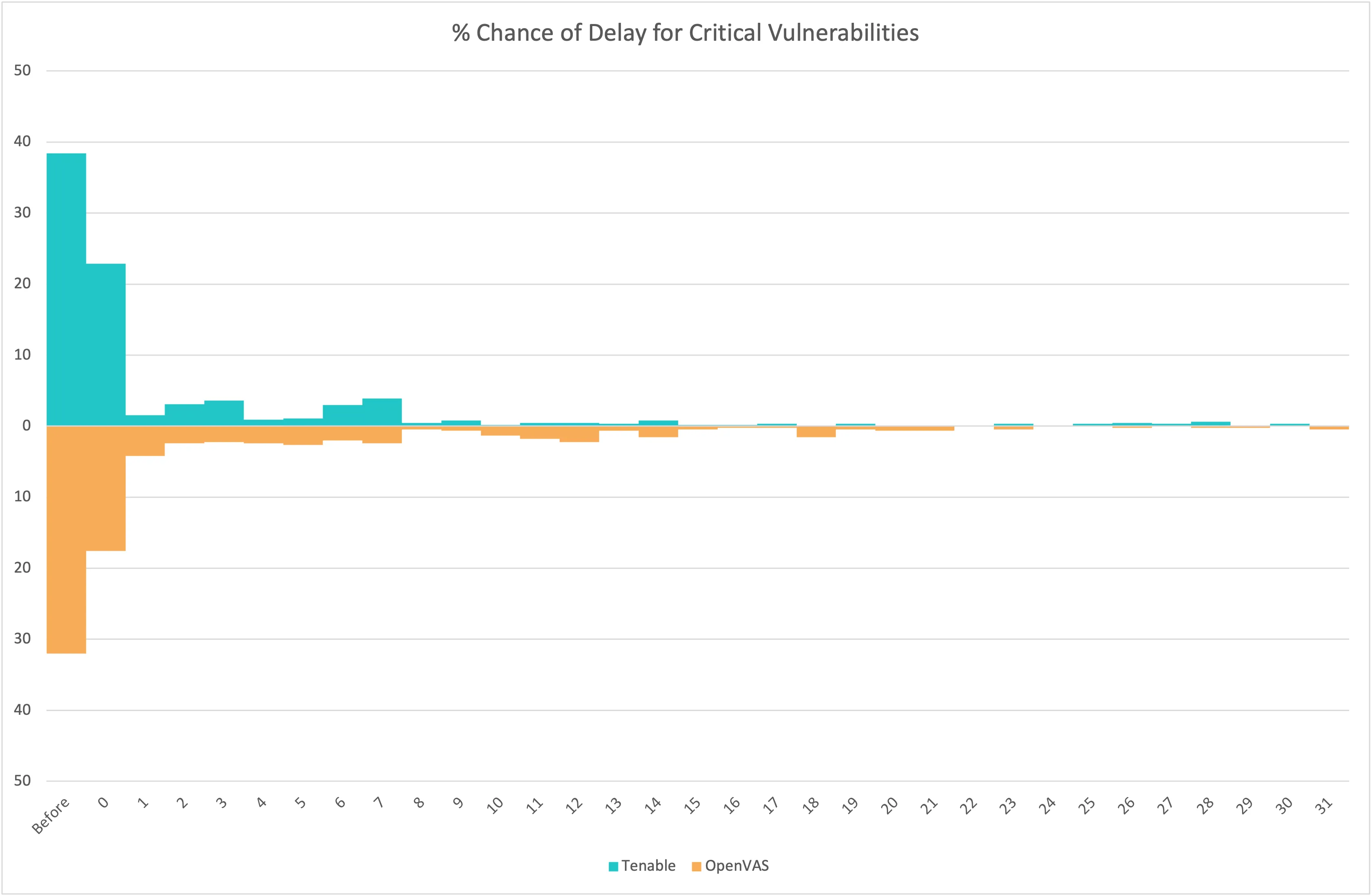
65 new vulnerabilities are discovered almost every day. Most businesses don’t have the time or expertise to stay on top of them – and they have little time to protect themselves from any weaknesses being exploited following new checks or vulnerabilities. Two features of our new Premium plan are designed to address this challenge: Rapid Response and priority ETS (Emerging Threat Scans).
Rapid Response covers weaknesses ‘in the wild’, where you have a very small window to act before hackers can exploit them. Intruder continuously monitors security threat news feeds for emerging critical weaknesses where checks are not in place yet. So, when attackers are alerted to emerging vulnerabilities, we are too - and our security team is already checking your systems for them. Where exposed servers are discovered, you'll receive advisories with details and recommendations that help reduce your time to fix.
When information is published about critical weaknesses, we scan your network within one working day of exposures hitting the news streams. As a Premium customer, you’ll also be scanned first. You don't have to do anything – scans kick off automatically, and once the scan is complete, we let you know if you’re all clear or whether you need to take action, via email, Slack or Teams, and in your Intruder dashboard. Where exposed servers are discovered, you’ll receive actionable advice, with details and recommendations to reduce your time to fix serious weaknesses.
Get the best support in the business
We know how important customer support is for customer success. That’s why Premium plan customers get a Customer Success Manager (CSM) as your dedicated point of contact for everything related to your account.
Your CSM is your trusted advisor and advocate at Intruder, working closely with you to understand your specific needs and goals. You’ve also got priority access to our Technical Support Specialists for expert support for any technical issues or operational questions.
Build your perfect plan with Bolt Ons
Need something extra? Want more specialist support or assurance? No problem. Boost Premium with additional extras to fit your specific needs.
- Bug hunting: when you need the extra assurance of a manual investigation, our security experts use the latest pentesting techniques to check for issues that the scanner can’t find. We focus on discovering the high impact attack chains that could severely affect your business if left unresolved, sending your advisories for any security issues that are discovered during the hunt.
- False positive reduction: don’t waste precious time sorting false positives generated by automated scans, let our security experts do the hard work so you can focus on the issues that need patching
- Weak credentials: we can continuously check your Microsoft 365 accounts for weak, common or default passwords before attackers can find and exploit them
Take the path to continuous cyber security
Simply being proactive is no longer enough to secure your systems. Continuous cyber security is now a necessity to protect your business, your customers and your reputation. With the launch of our Premium plan, we’re making continuous coverage a reality for every business. Get in touch and book a quick call to find out more.