Key Points
By scanning more frequently, the latest updates to Network View give more comprehensive and up-to-date visibility across your entire IT environment to take your network security to another level.
Decoupling network and vulnerability scanning
Helping customers reduce and protect their external attack surface has always been a priority at Intruder. Exposed systems offer the path of least resistance for hackers, who are continuously scanning the internet searching for an easy way to get in. The best way to protect your organisation is to monitor your assets continuously and control what is accessible from the outside.
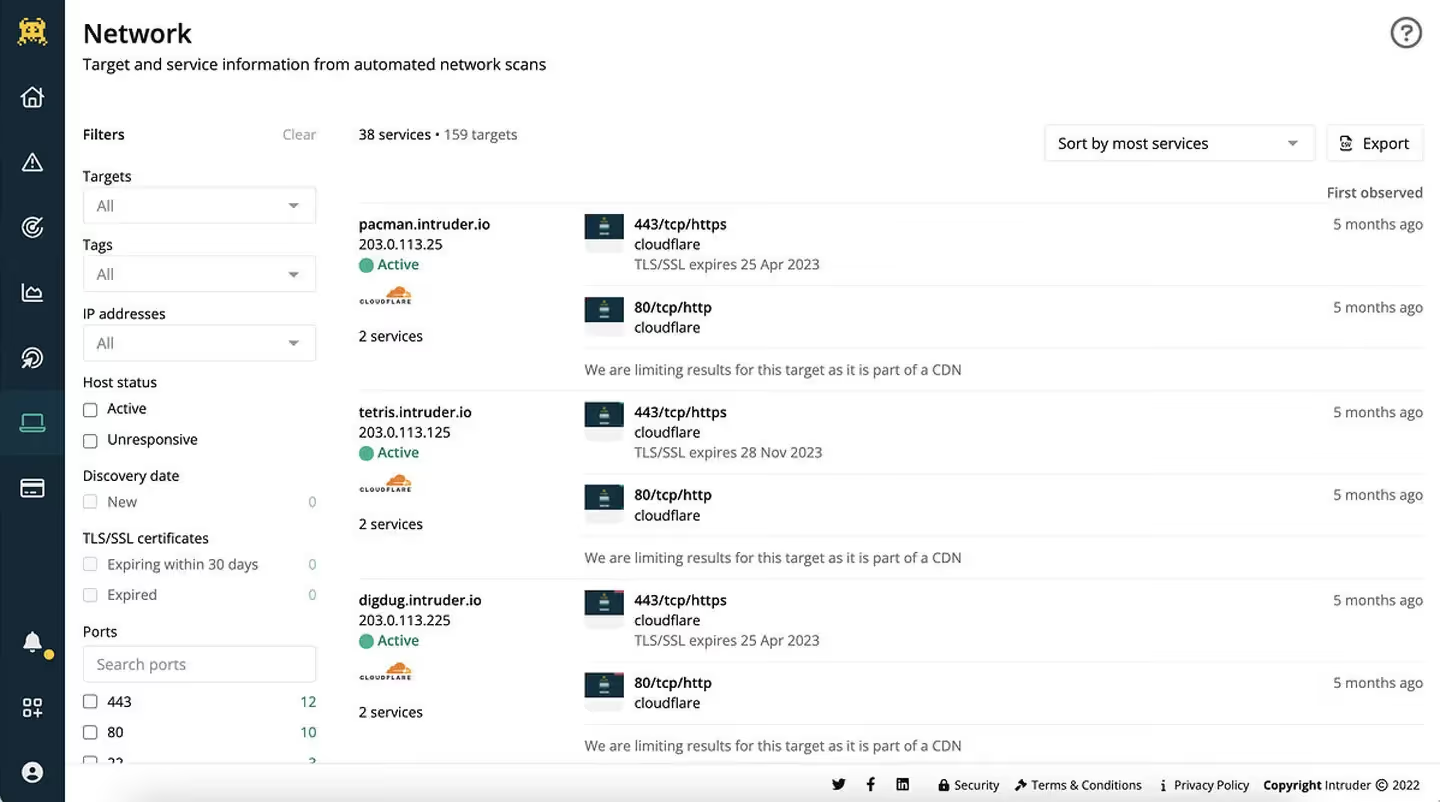
That’s why we run network scans across your environments in addition to vulnerability scans, to give you a detailed view into your entire external attack surface. Network View increases the visibility and transparency of your network, so you can mitigate the risk of possible cyberattacks by simply removing things that do not need to be there.
Introducing continuous network scanning
Over the past few months, we’ve made a number of big improvements we think you’ll love. Improvements to how Network View operates under the hood and in the user interface, and we’re excited to finally share them with you.
Get the most up-to-date view
Modern environments are dynamic and complex. If you have a large network, it can be particularly difficult to keep up with and on top of continuous changes. To make it easier, we’ve decoupled network scanning from vulnerability scanning and increased the frequency of network scans for Vanguard customers, giving you the most up-to-date view of your attack surface.
See what attackers can see
- Increase visibility: Network View will now be more up-to-date, so you have a clearer picture of what attackers can see and what’s accessible in your internet-facing infrastructure so you can easily hunt for services that could expose you to risk
- Preview your web assets: identify any web services that don't belong on the internet visually rather than text, such as exposed admin panels or login pages. In addition to dynamic filters, you now get visual screenshots of web services of what’s exposed to the internet rather than text-based notifications.
- Stay on top of changes: Intruder integrates with messaging and collaboration tools like Slack to notify your technical team about important changes to your network as soon as they happen. You can even choose the type and frequency of updates.

- React even faster: when new zero-days are discovered, Network View will now help identify your risk and limit your exposure to the maximum extent possible, even when there is no official vulnerability check available, like the recent OpenSSL vulnerability.
Watch this space
Continuous network scanning is just the start of our mission to deliver continuous monitoring. It lays the groundwork for further updates already in the pipeline, like allowing you to launch a vulnerability scan automatically when Intruder’s continuous network scans detect a change in your attack surface.
This, together with other planned features and functionality, will provide the powerful scanning you need for effective attack surface monitoring.
Still getting to know the network scan functionality? Check out our knowledge base article to learn how you can action the most critical information, or try Intruder for free today.










.avif)


