The Wiz alternative for lean security teams
Wiz is built for global enterprises with massive budgets and complex infrastructure. Intruder gives lean teams the same powerful cloud, application, and attack surface protection - delivering everything you actually need at a price that makes sense.
Built for teams that need to move fast
Wiz provides deep visibility into cloud environments through its Security Graph, showing relationships across your infrastructure. That level of detail serves enterprises managing complex, multi-cloud environments at scale.
Intruder focuses on speed and clarity. It continuously identifies exposed assets, highlights real-world risk, and prioritizes issues so teams can act quickly. You get comprehensive protection across cloud, applications, and attack surface without requiring specialized cloud security expertise or enterprise-level budgets.

React to threats faster
When high-impact vulnerabilities emerge, speed is everything. Intruder scans for them automatically, so you never have to wait for your next scheduled run to find a critical gap.
Minimal setup and tuning
Get value in minutes, not months. Intruder works out of the box without requiring dedicated cloud security engineers.
Clear answers, not more dashboards
Move beyond complex security dashboards. Intruder delivers prioritized results with the context your team needs to act fast.
Trusted by thousands of companies worldwide































































See risk clearly across your environment
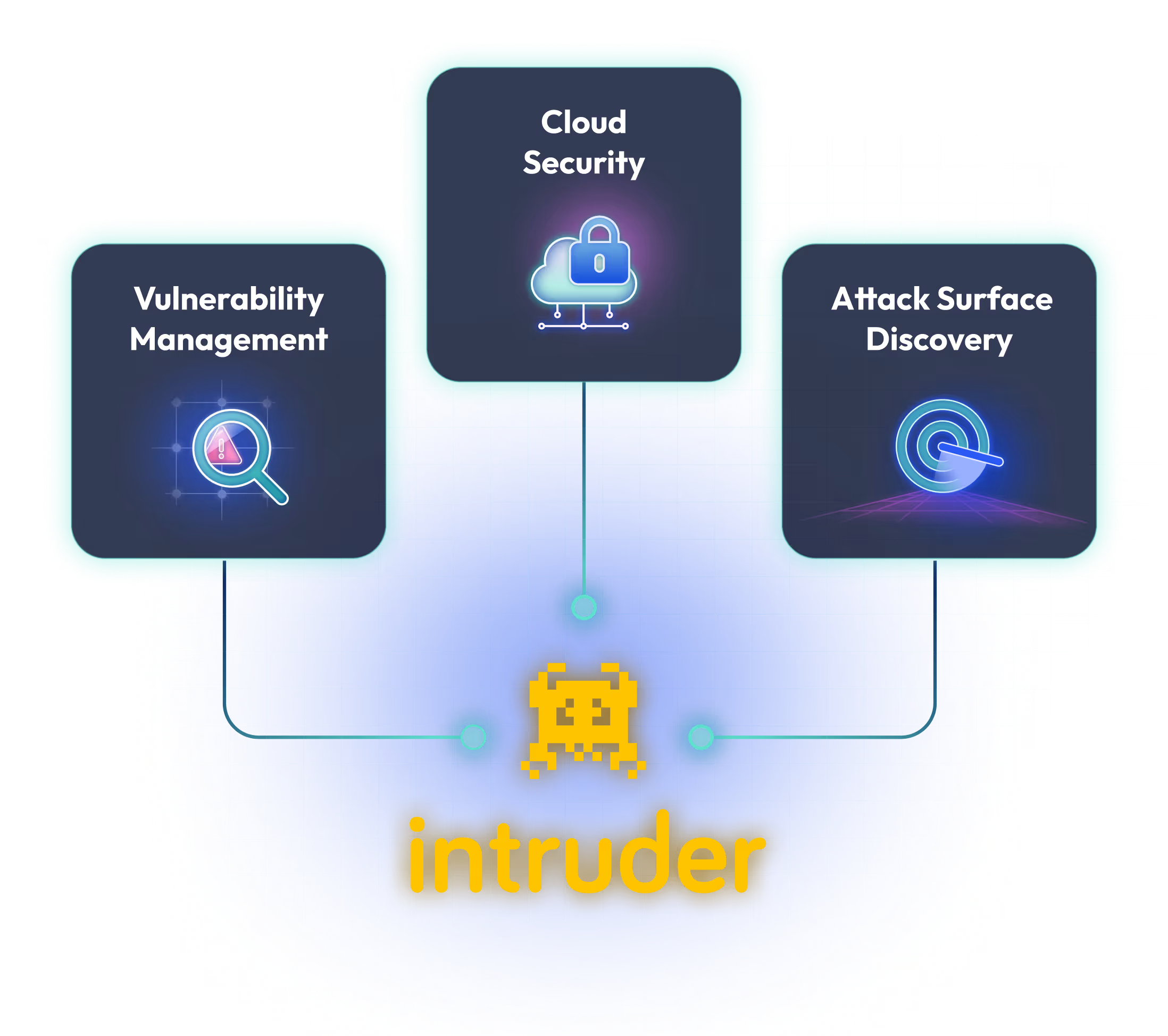
Intruder brings vulnerability management, attack surface management, and cloud exposure into one live view. Instead of juggling multiple tools, teams get a clear picture of what is exposed and what needs attention, with one workflow to manage it.

Know exactly what's broken, not just exposed
Wiz analyzes cloud configurations and relationships to assess risk. Intruder combines cloud configuration audits with active vulnerability testing of exposed services, web applications, and APIs. This means you get both configuration insight and concrete proof of exploitable vulnerabilities with clear steps to remediate them.
Automatically detect internet exposed assets
Intruder continuously maintains an up-to-date view of internet-facing assets across cloud and external environments, uncovering unknown services and Shadow IT. As environments change, new domains, APIs, and cloud resources are added automatically, so teams always work from a complete and reliable inventory.


Stay ahead of risk as environments change
Intruder doesn’t just monitor your cloud - it acts on change. Our adaptive scanning automatically triggers a vulnerability scan as soon as a new asset is discovered or a critical configuration shift is detected, such as an open port or modified security group. This ensures new risks are resolved within hours, without waiting for your next scheduled review.
Focus on what attackers can actually exploit
Visibility is only useful if it leads to action. Intruder prioritises findings based on exploit likelihood and contextual risk, helping teams concentrate on issues attackers are most likely to leverage, not low-impact configuration noise.


From finding to fixing, fast
Intruder connects to your existing tools like Slack, Jira, and GitHub, to keep remediation moving. GregAI triages findings and drafts plain-language notes so your team can fix issues fast without needing to be security experts.
Intruder checks your systems for 75+ web-layer security problems (such as SQL injection and cross-site scripting), 140,000+ infrastructure weaknesses (such as remote code execution flaws), and other security misconfigurations (such as weak encryption configurations, and systems which are unnecessarily exposed). Learn more about what checks we run.
Intruder’s emerging threat scans check your systems for newly discovered vulnerabilities automatically. This kind of proactive action is essential for businesses that don’t have processes in place to research the latest threats and manually run scans for them. Learn more.
Our team of experienced penetration testers will seek to identify serious weaknesses in your external targets that are undetectable by scanners. Continuous penetration testing is a bolt-on service available to Enterprise users and is sold and booked by the day. Learn more.
Intruder is powered by industry-leading scanners, including Tenable, Nuclei, OpenVas, and ZAP. Learn more.




