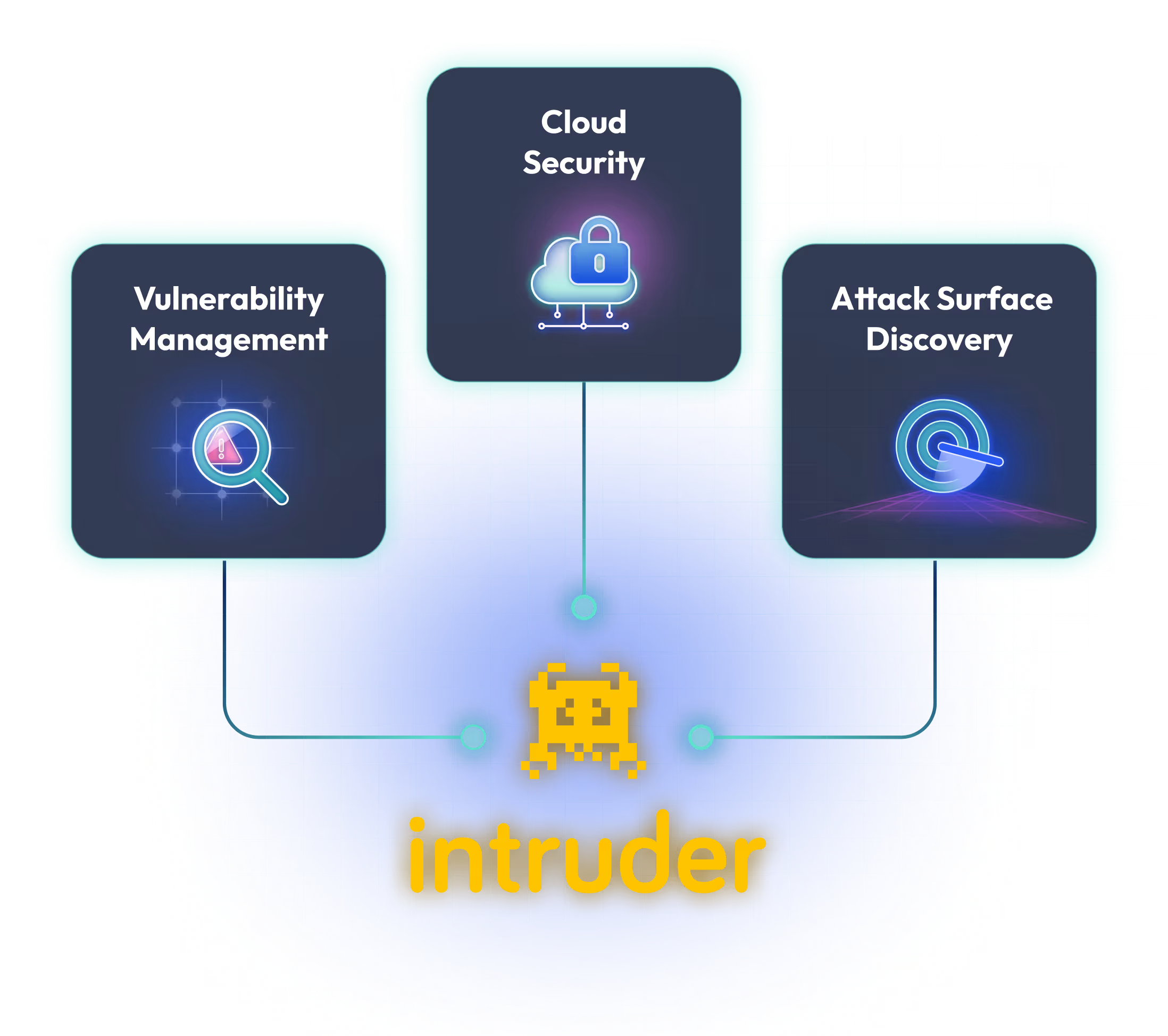
Proactive cloud attack surface management
Stay on top of your changing cloud environment. Intruder unifies asset discovery, container scanning, and configuration auditing across AWS, Azure, and Google Cloud to surface and prioritize your most critical exposures.
See what our customers say about us



Richard Grey
CISO
Thousands of happy customers worldwide































































Know what's exposed across your entire cloud estate
Intruder syncs with your cloud accounts every two hours, automatically discovering and scanning new services as they appear. Your inventory stays current as you scale, eliminating the need for manual updates or spreadsheet tracking.

.avif)
Detect vulnerable container images before they reach production
Automatically detect and scan new images in AWS ECR, Azure ACR, and Google Cloud Artifact Registry. When a new image version is pushed, Intruder detects the change and scans it automatically, helping you catch vulnerabilities before and after deployment.
Be alerted the moment your attack surface changes or a zero-day hits
Every time a port opens, a configuration changes, or a new service goes live, your attack surface shifts. And when a critical vulnerability drops, you need answers fast. Intruder detects surface changes and proactively scans as soon as new checks are available, so your coverage never falls behind your deployments.

Catch the misconfigurations driving your exposure
An exposed service is often the symptom of a cloud misconfiguration. Intruder runs daily agentless checks across your multi-cloud accounts to find overly permissive security groups, misconfigured IAM roles, or storage buckets left open before attackers do.
A single view of risk across your digital estate
Intruder brings asset discovery, configuration auditing, and vulnerability scanning into one prioritized view across AWS, Azure, and Google Cloud. Findings route directly to Jira, Slack, or Azure DevOps with clear remediation guidance, so your team can act without switching between cloud-native consoles and standalone scanners.

Read our reviews on G2.com





Cloud attack surface management is the process of discovering, monitoring, and securing cloud assets exposed to the internet. It covers asset discovery across cloud providers, configuration auditing, vulnerability scanning, and continuous monitoring for changes that increase exposure. The goal is cloud attack surface reduction: shrinking the number of exploitable exposures across your cloud environment.
Intruder supports AWS, Microsoft Azure, and Google Cloud for cloud sync and daily posture checks. It also integrates with Cloudflare for DNS-based target discovery. Cloud features are available on Cloud, Pro, and Enterprise plans.
CSPM audits cloud configurations for misconfigurations and policy violations. Cloud attack surface management is broader: it adds asset discovery, vulnerability scanning of exposed services, and continuous change monitoring. Intruder combines both in one platform.
No. Intruder combines cloud asset discovery, daily configuration checks, and vulnerability scanning (including web application and API testing) in one platform. 1,000+ attack surface checks and 170,000+ infrastructure checks, from a single prioritized view.
Yes. Intruder generates audit-ready reports for SOC 2, ISO 27001, HIPAA, and more, syncing evidence directly with platforms like Drata and Vanta.

