The simpler way to run a CTEM program
Get full-cycle CTEM without stitching together tools or having to scale your team. Intruder unifies discovery, prioritization, and validation into one manageable workflow.
Thousands of happy customers worldwide































































Always know what’s exposed
Your attack surface changes constantly - new cloud services, forgotten subdomains, inherited infrastructure. Intruder continuously discovers internet-facing assets across your cloud accounts and external perimeter, so your inventory stays current without manual effort.


Clear the noise, focus on what matters
Stop triaging hundreds of findings to find the ten that matter. Intruder shows you which exposures attackers are most likely to exploit, and when a critical vulnerability hits the news, you'll know within hours whether your environment is affected.
Confirm fixes actually worked
Prioritization tells you what to fix. Re-scans tell you whether you did. Intruder verifies that remediated issues are actually resolved, so your team isn't marking tickets closed on trust.


Track fixes, prove progress
Avoid the security bottleneck by routing findings directly to Jira or Slack with GregAI-drafted notes for your engineers. Your Cyber Hygiene Score provides the simple, high-level metric you need to show the board that your team is resolving issues and your security posture is actually improving.
CTEM without the complexity
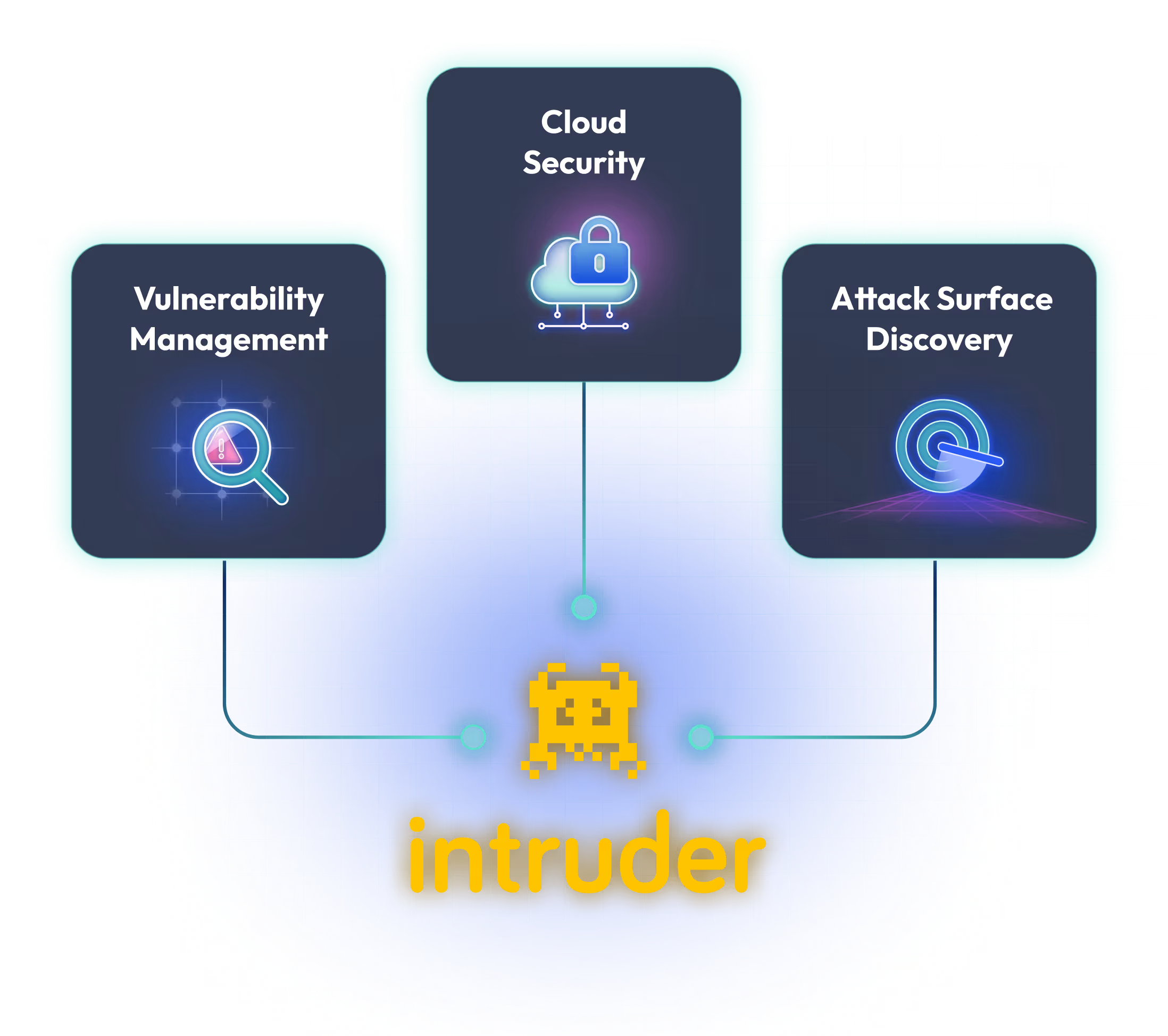
Most teams piece together separate tools for vulnerability management, attack surface management, and cloud security, then try to run a continuous program across all of them. Intruder brings all three into one platform, so running CTEM is straightforward instead of a project in itself.

Read our reviews on G2.com





Continuous Threat Exposure Management (CTEM) is a five-stage framework introduced by Gartner that helps organisations continuously scope, discover, prioritize, validate, and mobilise against exposures. Unlike periodic scanning, CTEM operates as a continuous cycle.
Vulnerability management focuses on software flaws; CTEM is a broader framework including misconfigurations and exposed assets, with explicit stages for validation and mobilization.
Intruder provides capabilities across each stage: scoping through automated cloud asset sync, discovery of subdomains and services across your perimeter and cloud, prioritization based on exploit likelihood, validation through active scanning and re-scans, and mobilization through workflow integrations and hygiene scoring.
Exposure management is the practice; CTEM is the Gartner framework that structures it into five repeating stages. Intruder supports both.
Yes. Intruder generates audit-ready reports for SOC 2, ISO 27001, HIPAA, and more, syncing evidence directly with platforms like Drata and Vanta.




