Key Points
“A new CVE appeared weeks after deployment. We had no idea our containers in EKS were affected."
It's a common blind spot. Businesses running containerized workloads often have limited visibility into what's inside their images. Vulnerable open source packages, outdated dependencies, and known CVEs go undetected — leaving a major gap in attack surface coverage. Traditional agent-based solutions exist, but they're complex to configure and maintain.
Intruder Container Image Scanning closes that gap. It automatically discovers your container images from AWS, Azure, and Google Cloud, and continuously scans the tags you choose to monitor.
Agentless container image scanning
Using registry level integrations with cloud providers, customers won’t have the operational overhead associated with deploying agents to nodes, maintaining and debugging them. A greatly reduced configuration burden means stretched security teams get time back to focus on fixing issues.
Coverage across all environments
Agent-based configurations are commonly used in environments like Kubernetes, but containers are also used across many components in cloud infrastructures, such as Functions as a Service (AWS Lambdas), Containers as a Service (AWS ECS), or directly inside virtual machines that also need to be scanned to avoid risks.
By scanning at the registry level, Intruder extends coverage to images deployed to managed container services where a lack of access to the underlying nodes would inhibit the deployment of agent-based solutions.
More signal, less noise
Most container vulnerability scanning tools scan every image version ever pushed to your registry — whether it's running in production or was replaced three deploys ago. The result? Alert fatigue and a security team that starts ignoring findings.
Instead of scanning everything, you choose which tags to monitor — typically the ones that reflect what's deployed. When you push a new version behind the same tag, Intruder detects the change, rescans it, and tracks the remediation automatically. The old version disappears from your results because it's been replaced.
Detection before deployment
Unlike agent based approaches, registry level scanning allows users to detect issues before the image runs in production. This allows you to ship new updates with confidence.
How it works
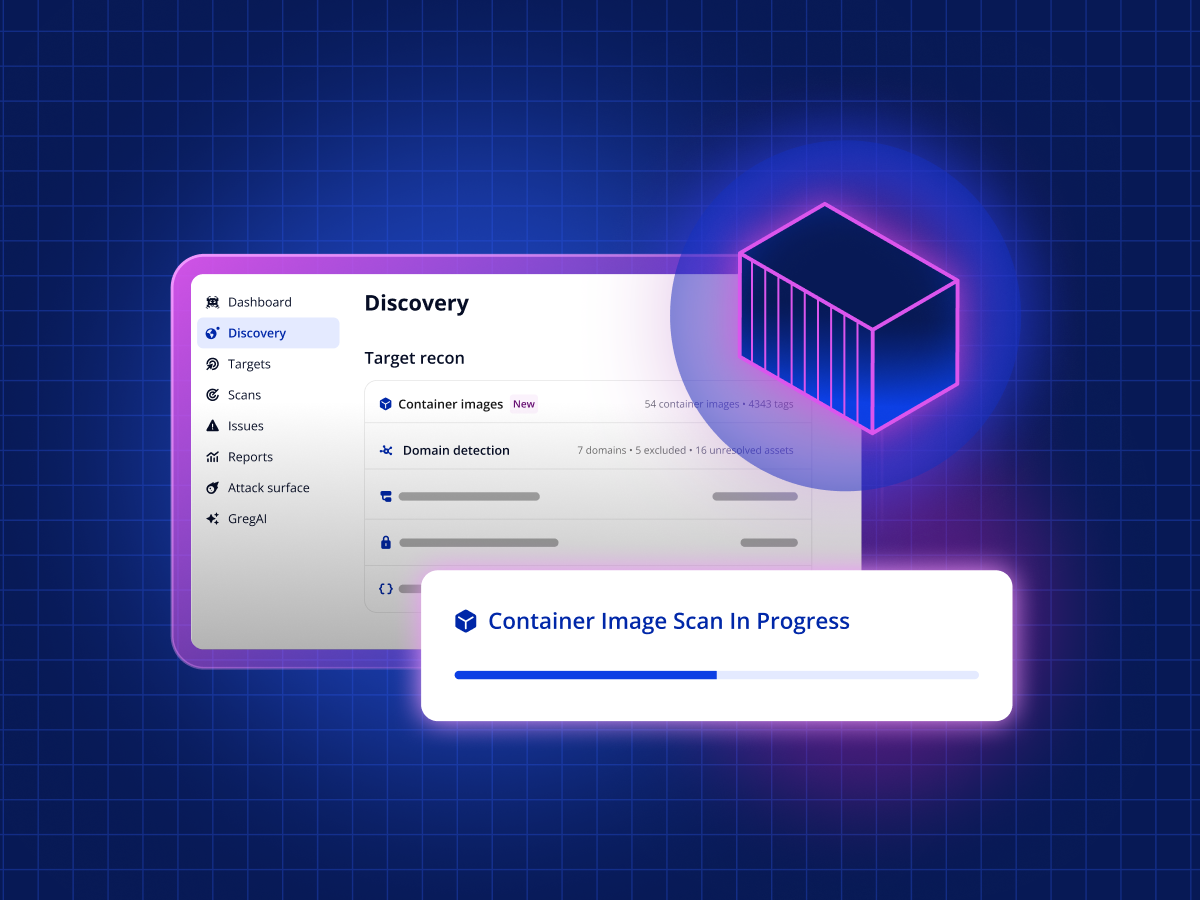
- Automatic discovery. Connect your AWS, Azure, or Google Cloud account and your container images (including Docker images) show up in your discovery view automatically. No agents required.
- One-click scanning. Pick a discovered image, tell Intruder which tag to monitor, and it becomes a scan target straight away. Scan results come back in less than five minutes.
- Continuous monitoring. Targets are rescanned every 24 hours. Push a new version? Intruder picks it up and scans it automatically. New CVE disclosed overnight? You'll know by morning.
- Prioritized results. Findings are ranked by real risk — exploitability, severity, and context — so you can focus on fixing the real threats.
Secure your container images today
Container Image Scanning is available now on the Cloud, Pro, and Enterprise plans. If you're already an Intruder customer with a cloud integration connected, your container images are waiting in your discovery view.
New to Intruder? Start a free 14-day trial or book a demo to see it in action.









.png)


