Key Points
Not every breach starts with a CVE. The entry point can be something as simple as an internet-facing admin panel, where a password gets guessed, reused from another breach, or socially engineered.
When a vulnerability does drop, anything affected and exposed to the internet is immediately at risk. Take MongoBleed (CVE-2025-14847) — it allowed attackers to steal credentials, API keys, and session tokens directly from server memory without authentication. At the time, more than 87,000 databases were publicly exposed that had no reason to be.
Most teams treat patching as the priority. But when a new CVE drops, the scramble to patch could have been avoided entirely if the software wasn't exposed in the first place. This matters more than ever now that AI models like Anthrophic’s Mythos can autonomously discover zero-days and time-to-exploit is down to a single day.
.png)
In our 2026 Attack Surface Management Index, we analyzed 3,000 attack surfaces to find out how widespread exposure is, what organizations are exposing, and how long it takes to remove it. Here’s what we found.
The types of attack surface exposures organizations are most exposed to
We grouped attack surface exposures into four categories and looked at the share of organizations affected by at least one issue in each. 60% of organizations had at least one HTTP panel exposed, 49% exposed a risky port or service, 42% had an exposed database, and 30% had files or information publicly accessible that shouldn't be.

The most commonly exposed port/service we identified was Remote Desktop (RDP), which is a concern given its prevalence as an initial access vector in ransomware attacks. RDP was notably affected by BlueKeep in 2019, a pre-authentication remote code execution vulnerability that left nearly a million systems immediately exploitable. If there’s a service that shouldn’t be internet-facing, RDP is the poster child.
We gave databases their own category because of how frequently they appeared, with MySQL being the most commonly exposed. Internet-facing databases have long been a target for opportunistic attackers. The PLEASE_READ_ME ransomware campaign in 2020 compromised more than 250,000 MySQL databases by brute-forcing weak credentials. MongoDB and Elasticsearch have faced similar attacks.
API documentation was the most common files and information exposure we found. While some API docs are intentionally public, organizations often overlook documentation tied to private or admin-side APIs that were never meant to be internet-facing. Our research found that public API documentation can turn otherwise undiscoverable API vulnerabilities into exploitable attack paths.
Get the full 2026 Attack Surface Management Index
The top 10 attack surface exposures
These are the most common attack surface exposures affecting organizations in the past 12 months.
- MySQL Database Exposed — 26%
- Postgres Database Exposed — 16%
- API Documentation Exposed — 15%
- WordPress Admin Panel Exposed — 15%
- Remote Desktop Service Exposed — 11%
- SNMP Service Exposed — 9%
- phpMyAdmin Admin Panel Exposed — 8%
- UPnP Service Exposed — 8%
- NTP Service Exposed — 7%
- RPC Portmapper Service Exposed — 7%
Exposed databases take the top two spots, with more than a quarter of organizations exposing MySQL and Postgres affecting 1 in 6. API documentation ranked ahead of RDP, with more than 1 in 7 organizations exposing it publicly. The remainder of the list is made up of legacy services designed for internal networks that were never meant to be internet-facing, including SNMP, UPnP, NTP, and RPC.
As organizations grow, so does attack surface exposure
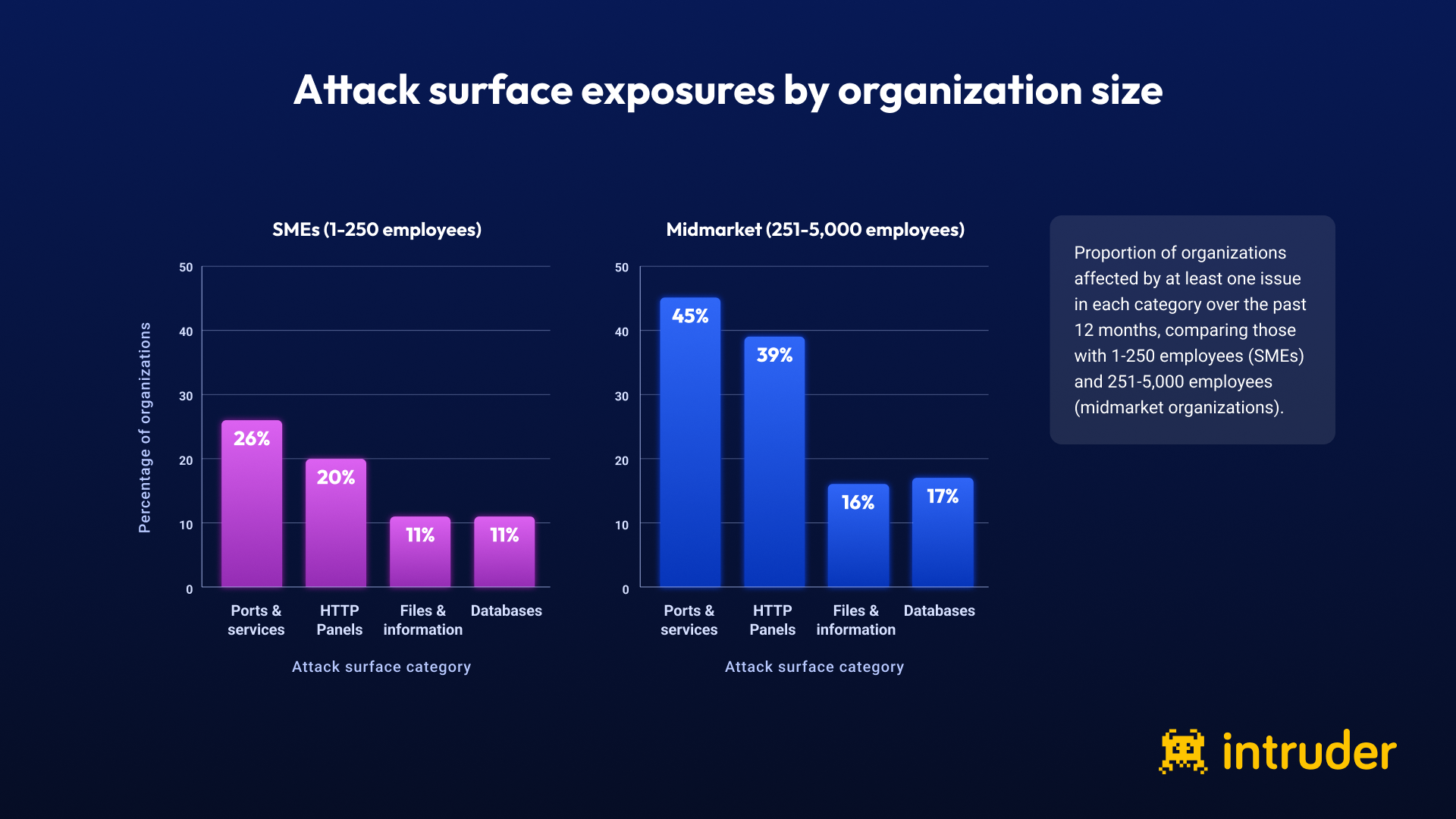
Among SMEs (1-250 employees), 54% had at least one attack surface exposure in the past 12 months, compared with 70% of midmarket organizations (251-5,000 employees).
The gap is consistent across every category. Among SMEs, 26% exposed risky ports and services, while 20% exposed HTTP panels. For midmarket organizations, those figures rise to 45% and 39%.
The number of exposed assets helps explain why. Organizations with 1,000-5,000 employees manage 748 assets on average — more than five times as many as organizations with 251-1,000 employees.
This is where attack surface management gets significantly harder: the infrastructure is scaling fast, but security teams, budgets, and tooling don’t always scale with it.
Midmarket organizations are slowest to remove exposures

Small organizations remove exposures fastest, taking 14-18 days on average. Remediation slows as companies grow into the midmarket, peaking at 56 days for organizations with 5,000-10,000 employees, before improving again at enterprise scale.
This is consistent with what we found in our 2026 Security Middle Child report: midmarket organizations have large attack surfaces but lack the headcount, budget, and tooling maturity of enterprise security teams.
Remove what’s exposed before it becomes a problem
Vulnerability management and attack surface reduction go hand in hand — but most teams focus on patching what's vulnerable, rather than questioning whether it should be exposed at all.
That’s why attack surface reduction should be a first step, not an afterthought. Intruder identifies over 1,000 attack surface exposures and prioritizes them alongside vulnerabilities, so teams can reduce and monitor their exposure over time. Since 2015, we've helped customers take more than 133,000 exposures off the internet.
Get the full 2026 Attack Surface Management Index for more insights and industry benchmarks.













