
Detect newly exposed assets and shadow IT before attackers do with automated attack surface discovery.
Keep eyes on your entire infrastructure and catch issues other scanners miss with emerging threat detection and change monitoring in addition to scheduled scans.
Connect your AWS, Azure and Google Cloud accounts to automatically detect and secure new cloud services and run daily misconfiguration checks.

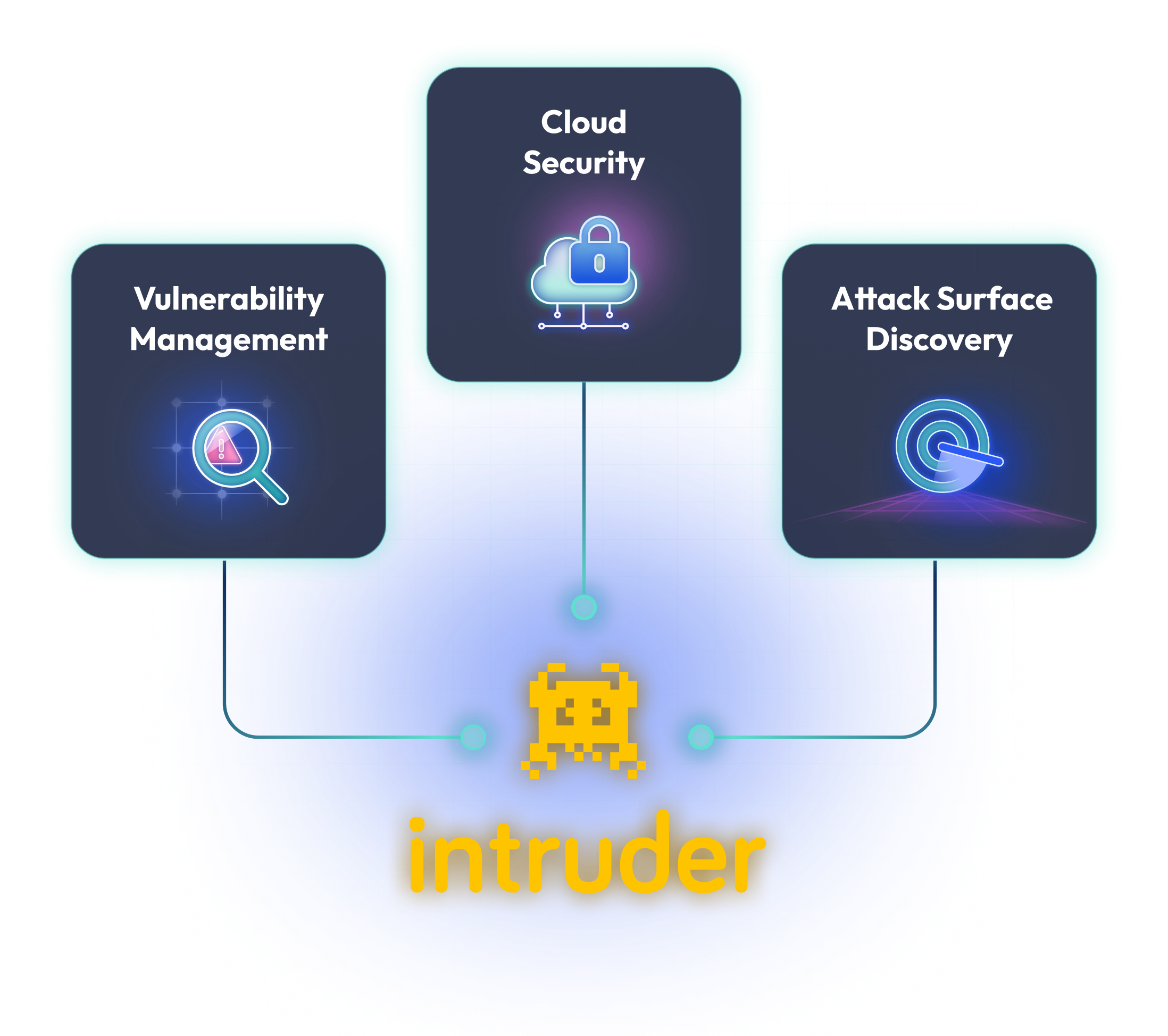
Infrastructure Security
Respond to changes
Daily cloud config checks
Reveal unknown targets
Secure web apps
No more alert fatigue
Demonstrate progress
Check and act fast
Automated image discovery
Prevent leaked credentials
140k+ checks
Test your APIs
SOC 2, ISO, HIPAA, DORA
Secure employee devices