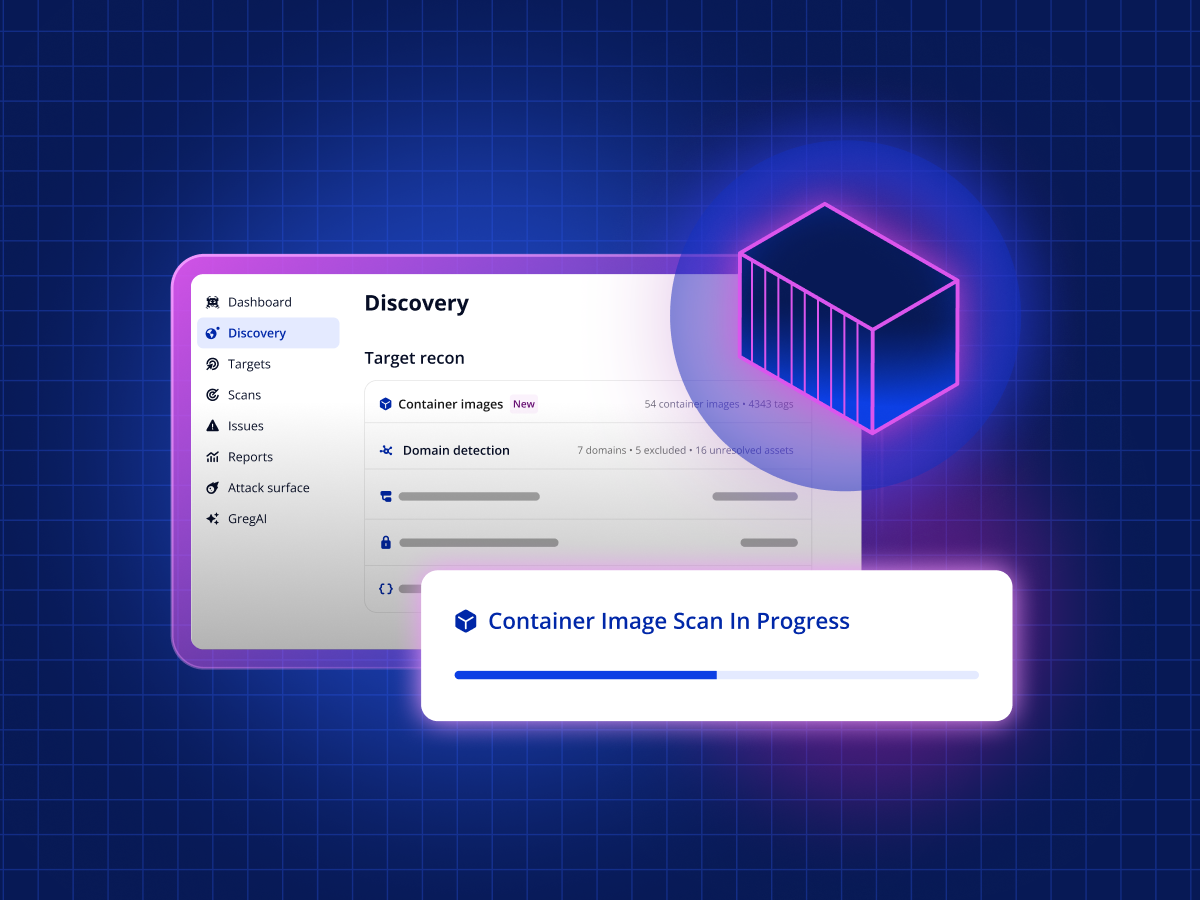
Introducing container image scanning: no agents, no blind spots
Agentless container image scanning. Automatically discover and continuously scan your container images across AWS, Azure, and Google Cloud. No agents, no blind spots.
Eamon Carroll
min read
April 9, 2026
min read

See TODAY’S CVE TRENDS
Our latest research
more research

Subscribe to the
Vulnerabulletin
Vulnerabulletin
.svg)

Cyber explainers
more guides
The Security Middle Child
How midmarket security teams are managing growth, complexity, and risk
get the report
Product news
more releases
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.